WP Cerber Security 2.9
What is new?
- Added ability to check and block prohibited usernames (logins). You can specify list of usernames (logins) on a new settings tab called Users. The plugin will immediately block any attempt to log in and will lock out any IP address have tried to use those logins. It’s recommended to have at least following usernames in the list: admin, administrator, manager, test. Defining this list you create a trap for brute force bots. Note: an attempt will be blocked even if user with one of those login exists on the site.
- Now you can specify rate limiting for notification letters. This setting tells the plugin how many letters can be sent per one hour (last 60 minutes). Set limit on the main settings page.
- Protection for wp-register.php and a custom login URL. If the new user registration has been disabled, automatic redirection from wp-register.php to the login page is blocked (will return HTTP 404 error). Remote IP will be locked out.
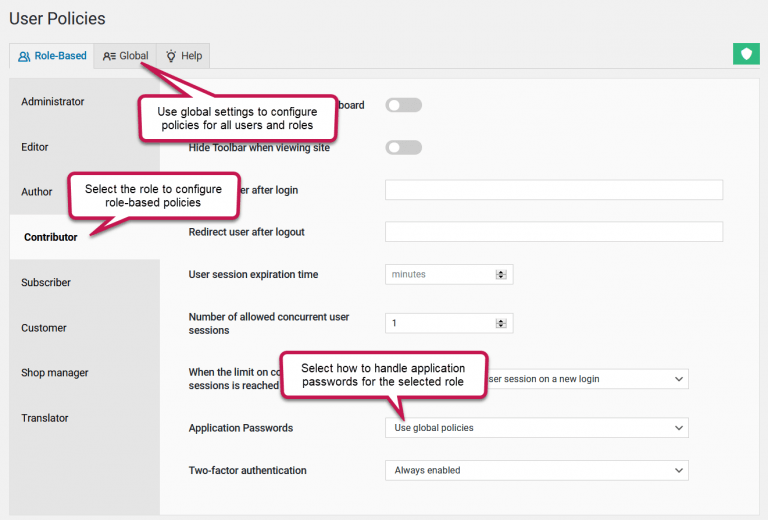
- You can set user session expiration timeout now. It defines how long user will stay logged in. Empty value do not change default WordPress expiration timeout.
- If you have unusual (and definitely weird) web server configuration you can define constant CERBER_IP_KEY and the plugin will use it as a key to obtain IP address from $_SERVER variable.
Minor changes and updates
- Update: Improved WP-CLI compatibility.
- Update: All dates are displayed in a localized format with date_i18n function.
- Fixed bugs: incorrect admin URL in notification letters for multisite with multiple domains configuration, lack of error message on the login form if IP is blocked, CSRF vulnerability on the import settings page
- Removed deprecated function get_currentuserinfo().
So, as you can see probably the best limit login attempts plugin is getting better!
Wonder what WP Cerber got in the previous version?
Review the release note for WP Cerber Security 2.7.2.
How to update WP Cerber
We recommend enabling automatic updates to ensure you always have the latest security features and performance improvements: how to enable automatic updates in the plugin settings.
How to install WP Cerber
New to WP Cerber? Follow this step-by-step guide to install WP Cerber on your WordPress.
Have any questions?
If you have a question regarding WordPress security or WP Cerber, ask it in the comments below or find answers on the community forum.
Spotted a bug or glitch?
We’d love to fix it! Share your bug discoveries with us here: Bug Report.
Releases
Next Post
WP Cerber Security 9.5
Releases



Great plugin! Keep up the good work!