WP Cerber Security Features
Armed with state of the art security algorithms Cerber Security effectively defends WordPress against hackers attacks and spam any kind
- Limit login attempts when logging in by IP address or subnet Class C
- Monitors logins made by login forms, XML-RPC, REST API requests, or auth cookies
- Restricts access with rich GEO country-based rules
- Restrict access with White IP Access List and Black IP Access List by IP address, IP range, or subnet
- Detects bots and hacker activity by using a set of traps and honeypots
- Malware scanner & WordPress integrity checker
- Automatic cleanup of malware and suspicious files
- Manage multiple WP Cerber instances from one dashboard.
- Traffic Inspector screens all suspicious requests and blocks them if they can harm a website.
- Log all activities related to the logging in and logging out processes
- Protects WordPress accounts with Two-Factor Authentication (2FA)
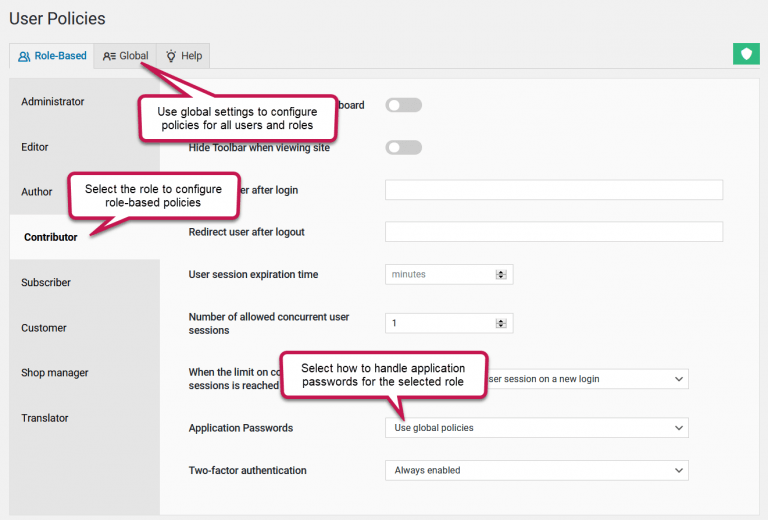
- Limiting the number of concurrent user sessions
- Spam protection: reCAPTCHA for WordPress and WooCommerce forms
- Hide wp-login.php from possible attacks and return 404 HTTP Error
- Hide wp-admin (dashboard) and return 404 HTTP Error when a user isn’t logged in
- Make Custom login URL for logging in (rename wp-login.php)
- Limits the number of allowed registrations from one IP address
- Managing WordPress application passwords done right
- Block WordPress user accounts
- Block user registration with a set of prohibited usernames or by specifying REGEX username patterns.
- Role-based access control for WordPress REST API
- Protects registration forms with reCAPTCHA and Cerber anti-spam and bot detection engine
- Immediately block IP or subnet when attempting to log in with non-existent username
- Disable automatic redirecting to the login page
- Disable WordPress REST API
- Disable XML-RPC: block access to the XML-RPC server including Pingbacks and Trackbacks
- Disable feeds (block access to the RSS, Atom, and RDF feeds)
- Restrict access to the XML-RPC, REST API feeds by White Access List by IP address, IP range or subnet
- Stop user enumeration via author pages
- Stop user enumeration via REST API
- Protection against (DoS) attack CVE-2018-6389
- Proactively block IP subnet class C for a suspicious IP address
- Citadel mode for massive brute force attack
- Play nice with fail2ban: write failed attempts to the syslog or a custom log file
- Provides an additional security layer with a special Cloudflare add-on
- View and filter out activity list by IP, username or a particular event
- Extra WHOIS information for IP: country, abuse contacts, network owner and much more
- Handles site/server behind a reverse proxy
- Configurable email notifications with rate limiting
Screenshots
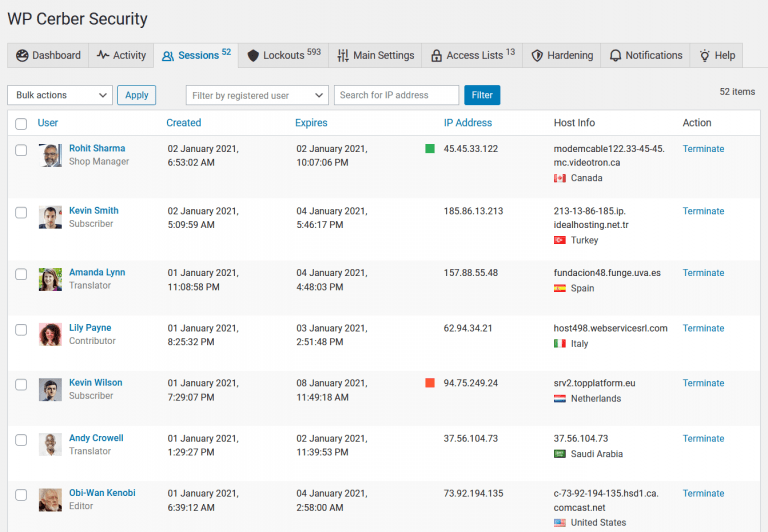
- A user session management console is a tool that enables WordPress administrators to manage user sessions on their websites from a central location. It allows administrators to search for, monitor, and manage active user sessions, including the ability to view user activity and terminate user sessions.
- The activity log in WP Cerber helps website owners and WordPress administrators monitor user activity, identify potential security threats, and troubleshoot issues that may arise on the website. The log search feature enables administrators to quickly find specific events in the activity log that they are looking for, such as failed login attempts or malicious IP addresses.
- On the Notification tab administrators configure email parameters for notifications, alerts, and reports. WP Cerber provides mobile alerts and email notifications to WordPress administrators to keep them informed about security-related events on their websites. Weekly and monthly security reports provide a comprehensive summary of security-related activity on the website and enables administrators to take proactive measures to prevent potential security breaches. To keep your WordPress plugins up to date, enable notifications when a new version of a plugin is available.
- A list of blocked malicious IP addresses is another tool for WordPress administrators. It provides a detailed overview of all IP addresses that have been blocked by WP Cerber, including host names, countries of origin, reasons for being blocked, and the ability to unlock an IP address if necessary. The blocked IP addresses are not allowed to log in, submit forms, or interact with the website in other ways. By clicking on a link in the Reason column, you will be directed to the activity log, which displays the malicious requests originating from the blocked IP address.
- On the Hardening tab you can manage multiple access control features that block access to sensitive website data, prevent user enumeration, disable user detail exposure, restrict access to WordPress REST API, and other WordPress data interfaces that are vulnerable to bad actors and data scraping bots. To monitor the usage of REST API, use the links at the bottom of the page.
- The Main Settings tab enables you to configure login security features, brute-force protection parameters, custom WordPress login page and other important plugin settings. Here WordPress administrators can configure the protection for the default login page, parameters of advanced and proactive security policies.
- The WP Cerber dashboard provides a real-time overview of important security metrics, displays activity of WordPress users, and shows important security events.