Why it’s important to restrict access to the WP REST API
A Critical bug in WordPress allows hackers to edit any post on your website easily.
Do you have a WordPress powered website? Congratulations! You offer a great tool for hackers. It’s called WordPress REST API and it is enabled by default. REST API is a technology that allows performing almost any action or administrative tasks on a website remotely. The WP REST API is enabled by default starting WordPress version 4.7.0.
Take control of REST API: How to restrict access to WordPress REST API
The WordPress REST API is not quite mature technology nowadays and its code contains plenty of unforeseen bugs. That’s why you need to restrict access to the REST API with a security plugin like WP Cerber. Please, take it seriously, guys, because I’ve got some bad news for you. Recently, right after a new version of WordPress 4.7 has been released, a critical bug has been found. This bug allows unauthorized visitors to edit any post on your website. The bug has been found by Ryan Dewhurst and has been fixed by WordPress team in WordPress 4.7.2.
The previous version WordPress 4.7.1 has been announced as Security and Maintenance Release and has fixes for eight bugs. Unfortunately, the REST API bug had not yet been fixed. That leaves unprotected millions of websites around the world. It’s hard to believe but updating WordPress on shared hostings may take up to several weeks. How many websites have been hacked and infected?
Meantime, since the REST API has been silently enabled for each website, 20 (twenty) bugs have been discovered and fixed. It’s quite a lot of bugs for technology that allows anyone to perform administrative tasks on a website in a background mode.
The WP Cerber Security plugin allows you to restrict or block access to the REST API completely. No matter how many bugs the REST API has.
Have any questions?
If you have a question regarding WordPress security or WP Cerber, ask it in the comments below or find answers on the community forum.
Spotted a bug or glitch?
We’d love to fix it! Share your bug discoveries with us here: Bug Report.




Does mail chimp have a rest api namespace that I should include?
RE: previous comment
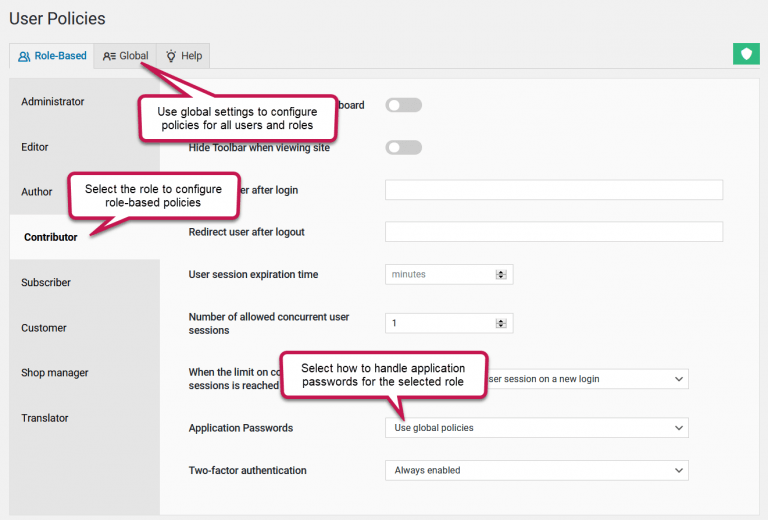
7. Restrict access to REST API and XML-RPC
Go to the Hardening admin page.
Check Disable REST API. Specify namespace exceptions for REST API if it’s needed. For instance, if you use Contact Form 7, the namespace is contact-form-7 for Jetpack it’s jetpack.
Please ask the mailchimp team. If their solution uses WordPress REST API in a way, they must know.
How do I establish what my enabled plugins name spaces are
You can easily find out the REST API namespace if you check a request URL and take a string between /wp-json/ and the next slash /. For example, here you can see the Contact Form 7 namespace which is contact-form-7: https://wpcerber.ru/wp-json/contact-form-7/v1/contact-forms/250/feedback