The WP Cerber scanner for WordPress
The scanner is a complete solution for monitoring file changes, verifying the integrity of WordPress, plugins, and themes, and for automatic malware removal for WordPress
A manual scan mode
To manually start scanning, go to the Site Integrity admin page and click either the Start Quick Scan button or the Start Full Scan button. Do not close the browser window while the scan is in progress. You can open a new browser tab to do something else on the website. Once the scan has finished, you can close the window; the results are stored in the website database until the next scan.
Depending on server performance and the number of files, the Quick scan may take about 3-5 minutes, and the Full scan can take about ten minutes or less.
During the scan, the plugin verifies plugins, themes, and WordPress by loading checksum data from wordpress.org and using local integrity data. If the integrity data is not available, which happens with a commercial plugin or a theme, you need to upload an appropriate source ZIP archive. You need to upload the archive once, after the first scan.
An automated scan mode
With Cerber Security Scanner, you can easily configure your own schedule for automated recurring scanning and automatic malware removal.
What’s the Quick Scan?
During the Quick Scan, the scanner verifies the integrity and inspects the code of all files with executable extensions only.
Well, what’s the Full Scan?
During the Full Scan, the scanner verifies the integrity and inspects the content of all files on the website. All media files are scanned for malicious payload.
Configuring the scanner
Configuring automated recurring scans
Configuring automatic malware cleanup and file recovery
Interpreting scan results
The scanner shows you a list of issues and possible actions you can take. If the integrity of an object has been verified, you see a green mark Verified. If you see the “Integrity data not found” message, you need to upload a reference ZIP archive by clicking “Resolve issue.” For all other issues, click on an appropriate issue link. To view the content of a file, click on its name.
By default, the scanner shows you short file names; to view full file names with their absolute paths, click the icon on the bottom right corner.
Dealing with suspicious files
The following states indicate a security issue with a file.
Checksum mismatch. The contents of the file have been changed and do not match what exists in the official WordPress repository or a reference file you’ve uploaded earlier. The file may have been infected by malware or has been tampered with.
Suspicious code found. During the code inspection with heuristic analysis, the scanner found suspicious code signatures and code instructions.
Potentially malicious code found. Most likely, this file contains malware because detected code signatures should not be in a file of this type.
Unattended suspicious file. The scanner recognized this file as “ownerless” because it does not belong to any known part of a plugin, a theme, or WordPress and should be deleted. It may remain after upgrading to a newer version of WordPress or some software you have. It also may be a piece of unknown obfuscated malware. In some rare cases, it might be a part of a custom-made (bespoke) software.
Content has been modified. This happens when a file has been altered, and the checksum of the file doesn’t match the checksum of the original file. You need to reinstall an appropriate plugin or theme.
Executable code found. A file contains executable code and may contain obfuscated malware. If this file is a part of a theme or a plugin, it must be located in the theme or the plugin folder.
If a file is marked as suspicious or malicious, you can open it safely to view the content of the file. To view the content of a file, click on its name.
Deleting files
You can usually delete any suspicious or malicious file if it has a checkbox in its row in the leftmost cell. Before deleting a file, click the issue link in its row to see an explanation. When you delete a file the plugin moves it to a quarantine folder.
Restoring deleted files
If you delete an important file by chance, you can restore the file from a quarantine folder. The location of the folder is shown on the Tools / Diagnostic page. This folder is not accessible from the Internet.
To restore a deleted file you need to use a file manager in your hosting control panel. The original name and location of the deleted file is saved in the .restore file. It’s a text file so you can open it in a browser or a file viewer.
Troubleshooting
If the scanner window stops responding or updating, it usually means the process of scanning on the server is hung. This might happen due to several reasons, but typically this happens due to a misconfigured server or some hosting limitations. Do the following:
- Try to disable scanning the session directory or the temp directory (or both) in the scanner settings
- Open the browser console (use the F12 key on PC or Cmd + Option + J on Mac) and check it for CERBER ERROR messages
- Enable diagnostic logging
Note: The scanner requires the CURL library to be enabled for PHP scripts. Usually, it’s enabled by default.
What does exactly the scanner scan?
- Scans and verifies all WordPress files
- Scans and verifies all plugins
- Scans and verifies all themes
- Detects not bundled, abandoned, and unattended files
- Inspects file contents for suspicious code signatures
- Inspects any files as if they were executable
- Inspects .htaccess files for malicious directives
- Scans all folders for new and modified files
- Scan all temporary and session folders
Read more about scans: What Cerber Security Scanner scans and detects
Does the integrity checker support commercial themes and plugins?
Absolutely. When you install a theme or a plugin, the scanner takes a snapshot of all files in the plugin or theme ZIP archive and uses it for integrity checking.
Does the integrity checker recognize the version of a plugin or a theme?
Sure! WP Cerber automatically detects which version of WordPress you are running and performs integrity checking with the appropriate version. This version detection and comparison with the correct version also applies to all themes and plugins.
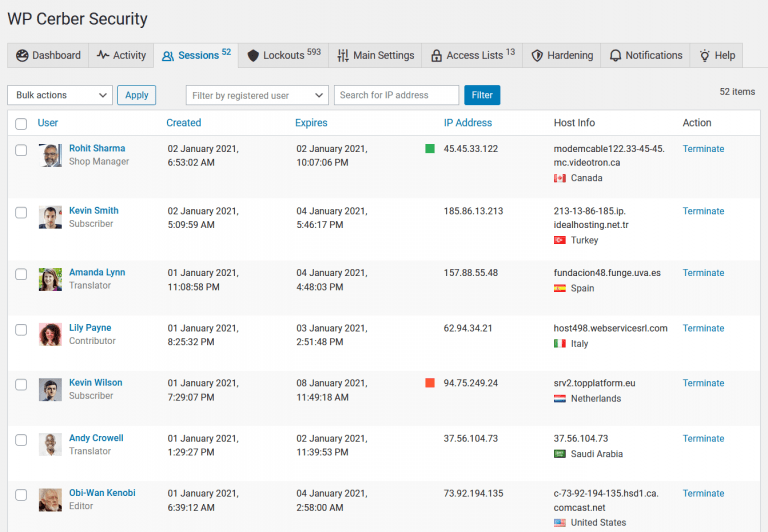
How to control the scanner on multiple websites
You can control and configure the scanner on any number of websites from one, main website. Enable a main website mode on the main Cerber.Hub website and a managed website mode on your other websites to control and monitor all WP Cerber instances from one WordPress dashboard.
Know more about the malware scanner
Automated recurring scans and email reporting for WordPress
Automatic cleanup of malware and file recovery
What Cerber Security Scanner scans and detects
Cerber Security Scanner Settings explained
Troubleshooting malware scanner issues
Have any questions?
If you have a question regarding WordPress security or WP Cerber, ask it in the comments below or find answers on the community forum.
Spotted a bug or glitch?
We’d love to fix it! Share your bug discoveries with us here: Bug Report.



Hello, I Scanned my site for curiosity and scanner found 1738 critical issues (high risk – Unattended suspicious) – almost all core WP files. Plugins – ok. Site working fine.
“It may remain after upgrading to a newer version of WordPress.”
I think this is too much 🙂 Searching for “true” issue in 1,5k files is… time consuming. I’m glad that You develop new feature. Thank You for great work. But at this point is really hard for beginners like me to find and recognize “true” critical issue.
Thank You again.
Hi Kris!
I think your website is quite old. I mean you have an aged website like seven years old or something and you started many years ago with one of the first versions of WordPress. Now you see a bunch of unattended files that remained from previous versions. Unfortunately, when WordPress upgrades itself it doesn’t clean up after it and now the scanner shows you those files. In the professional version of WP Cerber, you can enable automatic scanning plus scheduled cleanup of malware and old files including leftovers from the previous versions of WordPress. In the free version, you can delete a file manually by using a checkbox in the leftmost column.
Hello,
I did a full site scan, which revealed a number of issues. In resolving these, I received the following message back after trying to upload a plugin:
We have not found any integrity data to verify WP Rocket v. 3.5.5.1.
Uploading the file, please wait…
Processing the file, please wait…
Error: File wp-rocket_3.5.3.zip cannot be used. Proper program code not found or version mismatch. Please upload another file.
I have 2 questions about this:
1. Is the issue that my zip file is from the initial integration and not from the latest version? If this is the case, does this mean I have to try and get an updated zip file from the plugin owner?
2. If I do need to get an updated zip file, will I need to do this for every plugin that updates?
Thanks in advance!
1. Both versions of the plugin, installed on your website and the archive you’re uploading, must match exactly. In your case, it’s version 3.5.5.1.
2. To install a new version of a commercial plugin in a hassle-free way that is compatible with the integrity checker, you can use this nice plugin: https://wordpress.org/plugins/easy-theme-and-plugin-upgrades/
Hi,
I’ve using the WP Cerber Security plugin for a while, and did a full manual security scan every month.
After a few full scans I saw the Site Database growing (filled up to more than 80%) due to a huge amount of rows in the WP_Cerber_files table (more than 60.000).
I think every full scan all the checked files are handled as new, and the existing rows in the database aren’t matched and merged.
How to adjust this?
Thank you in advance.
Best regards,
That’s normal. You should not worry about this table. The scanner automatically removes outdated rows from the table and keeps the list of files from the last scan and the previous one. Since we use two types of scans, the table can hold up to four lists of files at most. If you use a plugin to back up your DB, you definitely should add the wp_cerber_files table to the list of tables not to back up.
I am new and still testing, but what is disturbing is that after every automated update of a plugin, the next scan does find a lot of errors in the plugin and the fix is to upload the ZIP file with the new version.
Does this mean that with Cerber I do need to run all plugin updates manually via uploading the ZIP file with the new version?
Not necessarily. Are you asking about updating a commercial plugin? What kind of software do you use to update the plugins?
It happend for example with Advanced Custom Fields PRO and All-in-One WP Migration as well as All-in-One WP Migration Unlimited Extension.
I do have Easy Updates Manager installed but did click on update now on the plugin page in WP when the message did show up that there is a new version available
For the plugins and themes installed from wordpress.org, please use the updating mechanism that is built-into WordPress. It’s completely compatible with the scanner. No manual actions are needed. You can enable automatic updates on the Plugins admin page, and both WP Cerber’s scanner and WordPress updater will work together seamlessly. If you want to update those plugins manually, use the “update now” links on the Plugin page. Both ways are fully compatible with WP Cerber’s scanner.
As for the commercial plugins and themes downloaded from vendor websites, you need to upload them from within the WordPress dashboard. This way is fully compatible with WP Cerber’s scanner too. For plugins: Plugins menu > Add new menu > Upload Plugin button. For themes: Appearance > Add new button > Upload Theme button.
I think Easy Updates Manager has a proprietary way of updating plugins and themes that is not compatible with WP Cerber. Do you use it to manage updates on multiple websites?
Thank you,
Yes I do use Easy Updates Manager on all sites, because I does allow to postpone WP core and Theme updates in the case that plugins which I use are not ready for the new version.
I see. We will implement those features in Cerber.Hub soon.