Why reCAPTCHA does not protect WordPress against bots and brute-force attacks
Using reCAPTCHA for WordPress login form is a bad practice and does not protect WordPress from being hacked by bots and hackers
What is reCAPTCHA, anyway?
Google’s reCAPTCHA is a human verification mechanism that created and maintained by Google as a free web service. WP Cerber supports reCAPTCHA for WooCommerce and WordPress forms as an anti-spam feature.
Why does reCAPTCHA not protect WordPress from bots and brute-force attacks?
It’s possible because WordPress has three authorization methods that enabled by default. That means hackers can exploit three entrances on any WordPress powered website. The first one is using the default WordPress login form. Two other methods are invisible for you but known for hackers and specialized software that hackers use. Cybercriminals use them for obtaining users’ passwords and consequently to get access to the WordPress Dashboard with admin privileges.
Any captcha-based mechanism, including reCAPTCHA, can protect WordPress against a brute-force attack to an ordinary login form only. The other two WordPress authentication methods are still unprotected. Why? Because reCAPTCHA is developed to protect websites from robots via a human verification mechanism. Hackers are not robots even if they use botnets. That’s why reCAPTCHA does not protect websites from being hacked.
I see plenty of plugins that offer using reCAPTCHA to protect login form. I have a question for you: do those plugins protect your website completely including the following two methods like WP Cerber does.
- Cookie-based authorization
- XML-RPC authorization
Does it mean reCAPTCHA useless?
Nope. reCAPTCHA can be successfully used as a spam-prevention mechanism for registration, contact, and password reset forms. Vital parts of WordPress must be protected with a specialized security solution only.
How do I protect my website from spam?
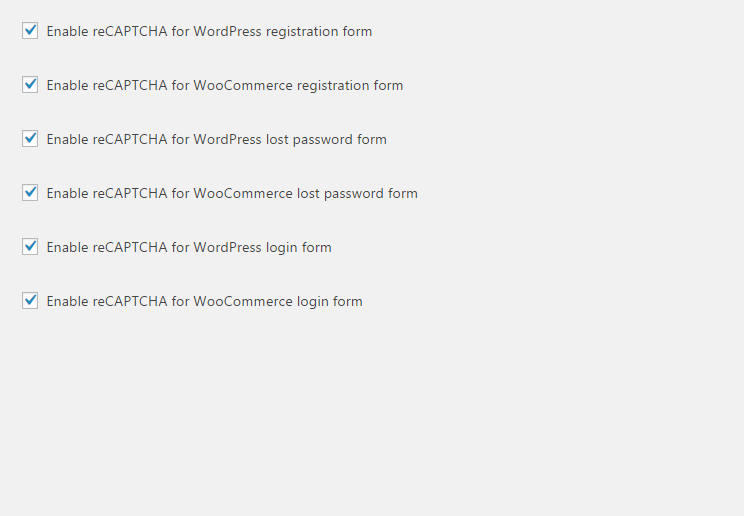
To protect WooCommerce and WordPress forms, WP Cerber Security offers two options
- Cerber antispam and bot detection engine, follow the instruction: Antispam protection for WordPress forms
- Using reCAPTCHA, follow the instruction: How to set up reCAPTCHA.
How to bypass reCAPTCHA
Is it possible that bots can solve reCAPTCHA without a human? Sounds unbelievable but they can do that by using an interesting method. The method is based on using voice captcha called Audio Challenge and one of those online speech recognition services like Google Speech Recognition API. A hacker takes an audio file with voice captcha generated by reCAPTCHA and then recognize it with a speech recognition service. Is not it brilliant?
This method has been discovered back in 2012. Fortunately, this method is not exploitable in real circumstances – when Google service identifies multiple attempts to solve the captcha from the same IP address, the voice captcha is changed into a more complex voice that cannot be identified using this approach. So, to successfully use this method hackers have to use a lot of IP addresses. To achieve that hackers can infect a significant amount of mobile devices with malicious software. But there is a question. Is the ability to post spam comments or register with a fake name on a website worth it? It’s easier to hire a bunch of guys from a poor country to do that manually in a bulk mode.
Want to know more? Subscribe to the Cerber’s newsletter.
Have any questions?
If you have a question regarding WordPress security or WP Cerber, ask it in the comments below or find answers on the community forum.
Spotted a bug or glitch?
We’d love to fix it! Share your bug discoveries with us here: Bug Report.




Yea because recaptcha was designed to be an antivirus or antimalware for your website. As far as I can understand recaptcha is to stop bots from abusing contact forms, login pages, etc etc. I don’t understand why someone would think recaptcha is for actually keeping the whole wordpress site safe. Fail article…
reCAPTCHA has not been designed to be an antivirus or antimalware tool. reCAPTCHA works fine with ordinary HTML forms that intended for being used by humans. It doesn’t protect APIs or other computer to computer interfaces.
This article is completely out of context. reCAPTCHA does exactly what it is supposed to do – protect forms from being submitted by bots. Doesn’t matter if they are login forms or any other sort of forms. If the intent of this article is to enlighten people about securing their WordPress installation completely, it needs to do a better job that attacking reCAPTCHA. I’d suggest loosing the preposterous tone!
Yes, reCAPTCHA does exactly what it is supposed to do – protect forms from being submitted by bots. Does someone say the opposite? When it comes to WordPress, having reCAPTCHA on its login form doesn’t protect the website from attackers because WordPress has three authorization methods. Using the login form is only one way of getting authorized on a website. Two other ways are used to authorize a user without a login form and therefore cannot be protected by reCAPTCHA. Unfortunately, many website owners have no idea about this security issue.