Brute-force, DoS, and DDoS attacks – what’s the difference?
These types of cyberattacks are well known since the beginning of the Internet. Do they pose a security risk for WordPress? What security tools can effectively mitigate them? What are the chances that we can do that successfully?
A Brute-force attack is a trial and error method used by hackers to guess credentials or encrypted data such as login, passwords or encryption keys, through exhaustive effort (using brute force) with the hope of eventually guessing correctly. The brute-force attack is one of the most popular password cracking methods for hacking WordPress.
A Denial-of-Service (DoS) attack is an attack meant to shut down a website or a web server, making it inaccessible to its intended users by flooding it with useless traffic (junk requests) from a single host (IP address). Sometimes DoS attacks are used for destroying computer defense systems. Some functionality of WordPress can be exploited as an attack vector for DoS attacks. For instance, CVE-2018-6389.
A DDoS attack is short for “Distributed DoS attack”. Such attacks are mounted by flooding the targeted website or web server with useless traffic from multiple devices or a botnet. A botnet is a network of computers infected with malicious software (malware) without the user’s knowledge, organized into a group, and controlled by cybercriminals. Modern botnets can contain tens of thousands of compromised mobile devices or desktop computers. Due to their nature, modern DDoS attacks are costly and require a lot of resources. Usually, that means you have a strong enemy that has enough gray money to order this kind of attack. Very often, mounting DDoS attacks are ordered by unscrupulous competitors or political opponents.
So, what’s the difference?
Technically they look different but from a website owner’s point of view, the difference is just in the goal of an attack.
Both, DoS and DDoS attacks have the same goal. And this goal is to push down the victim, the targeted website, or the web server and make a profit from that. Sometimes the DDoS attack is performing to destroy a defense system and obtain administrative access.
The goal of doing brute-force attacks is to obtain admin access to the targeted website to perform some illegal activity intruder/hacker wants to do. Their typical activities are:
- Redirecting legitimate users to fake websites to steal their personal data
- Creating phishing pages with payment forms that imitate legitimate ones on the victim website
- Stealing personal data from a customer database
- Installing backdoors and trojans on the webserver for using them as tools to attack other websites
- Installing malicious software to infect admin and customer computers
- Altering trustworthy website content to insert links to phishing websites
How do these attacks affect WordPress?
By default, WordPress allows unlimited login attempts through the login form, REST API, XML-RPC, or by sending special authentication cookies. This allows passwords to be cracked with relative ease via mentioned above brute-force attack.
How to protect WordPress and mitigate these attacks
Both brute-force and DoS attacks can be successfully mitigated with security software installed on a website. In both cases, you don’t need to be a nerd and can get that protection for free.
- Brute-force attacks against WordPress can be successfully mitigated by WP Cerber plugin. Among other security features, it protects XML-RPC and REST API interfaces.
- DoS attacks can be mitigated with a special web server configuration. You can’t achieve that by installing a security plugin. The best practice is using NGINX rate limiting rules. Check out our recommendations: Turn your WordPress into Fort Knox.
Unfortunately, DDoS attacks cannot be mitigated on a web server level or just with a WordPress plugin. DDoS attacks can be successfully mitigated only with special hardware installed on the hosting provider network. Due to their nature, mitigating DDoS attacks require a lot of computational resources and provided as a service from hosting providers on a subscription basis. Unlike brute-force and DoS attacks, there is no guarantee that all DDoS attacks will be successfully mitigated. Everything depends on how powerful the attack is, how powerful an anti-DDoS system is and what amount of network bandwidth the security provider can allocate.
One of the most affordable solutions for protecting WordPress from distributed DoS attacks is using Cloudflare services. But there are some disadvantages you should know and consider. Cloudflare will have control over all your DNS records for your domain, web traffic to and from your website including personal data of your customers because all traffic and all that data go through the Cloudflare proxy servers in unencrypted form. Some users reported that Cloudflare even had issues with owners being blocked out of their websites. So, if you have no issues with DDoS, like many of us, there is no reason to add one extra layer that can generate additional pain in the neck.
Once you’ve decided to go with Cloudflare, we recommend using a special Cloudflare add-on for WP Cerber.
Catch up an intruder
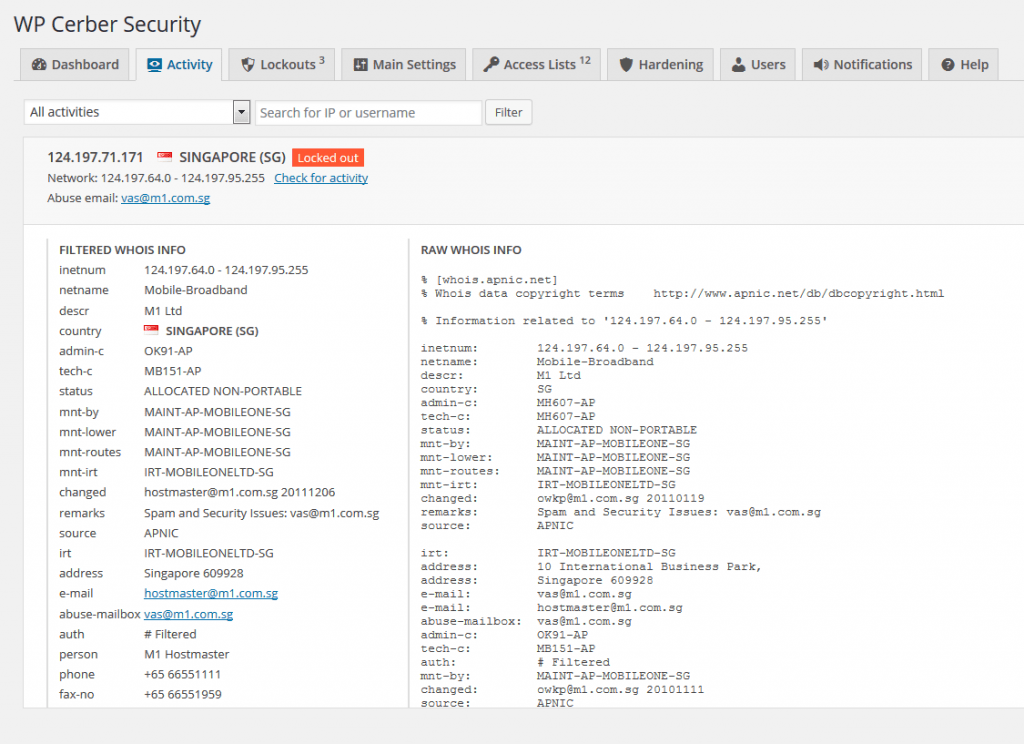
You can easily identify a physical source of an attack – a computer, a mobile device, etc.
If you have WP Cerber Security & Antispam installed, check out this post: Know more about intruder’s IP. The most disappointing thing is that the vast majority of those attacks cannot be traced back to a real performer or a master. Every attempt to trace them back ends up with a set of infected personal computers and mobile devices that are used as puppets, intermediate points for an attack.
Have any questions?
If you have a question regarding WordPress security or WP Cerber, ask it in the comments below or find answers on the community forum.
Spotted a bug or glitch?
We’d love to fix it! Share your bug discoveries with us here: Bug Report.