WordPress 4.7.1 – eight security issues have been fixed
Time to update! According to reports WordPress 4.7 and earlier are affected by eight security issues and now they are fixed
- Remote code execution (RCE) in PHPMailer – No specific issue appears to affect WordPress or any of the major plugins we investigated but, out of an abundance of caution, we updated PHPMailer in this release. This issue was reported to PHPMailer by Dawid Golunski and Paul Buonopane.
- The REST API exposed user data for all users who had authored a post of a public post type. WordPress 4.7.1 limits this to only post types which have specified that they should be shown within the REST API. Reported by Krogsgard and Chris Jean.
- Cross-site scripting (XSS) via the plugin name or version header on
update-core.php. Reported by Dominik Schilling of the WordPress Security Team. - Cross-site request forgery (CSRF) bypass via uploading a Flash file. Reported by Abdullah Hussam.
- Cross-site scripting (XSS) via theme name fallback. Reported by Mehmet Ince.
- Post via email checks
mail.example.comif default settings aren’t changed. Reported by John Blackbourn of the WordPress Security Team. - A cross-site request forgery (CSRF) was discovered in the accessibility mode of widget editing. Reported by Ronnie Skansing.
- Weak cryptographic security for multisite activation key. Reported by Jack.
Have any questions?
If you have a question regarding WordPress security or WP Cerber, ask it in the comments below or find answers on the community forum.
Spotted a bug or glitch?
We’d love to fix it! Share your bug discoveries with us here: Bug Report.
WordPress Security
Next Post
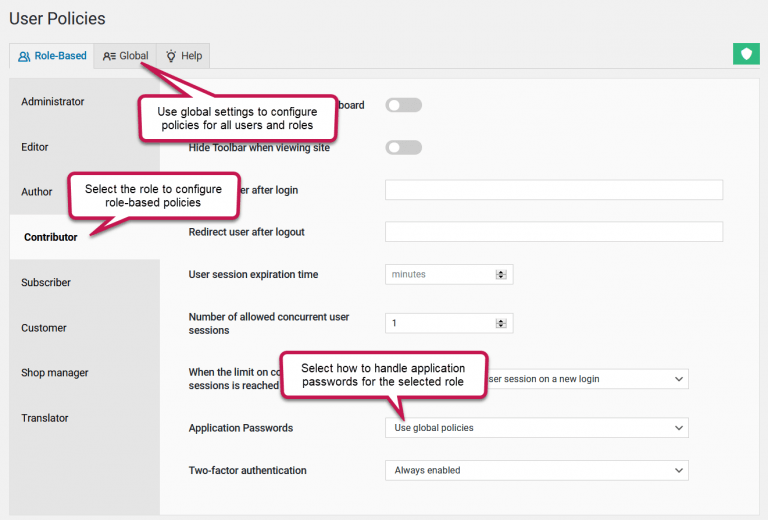
How to limit the number of concurrent user sessions in WordPress
Releases