Configuring exceptions for the anti-spam engine
Usually, you need to configure anti-spam exceptions if you use a technology that communicates with your website by submitting forms or sending POST requests programmatically. In such cases, WP Cerber can block legitimate requests because it can recognize them as generated by bots. This leads to false positives, which you can see on the Activity tab. Such log entries are marked as Spam form submission denied.
How to exclude specific requests from inspection
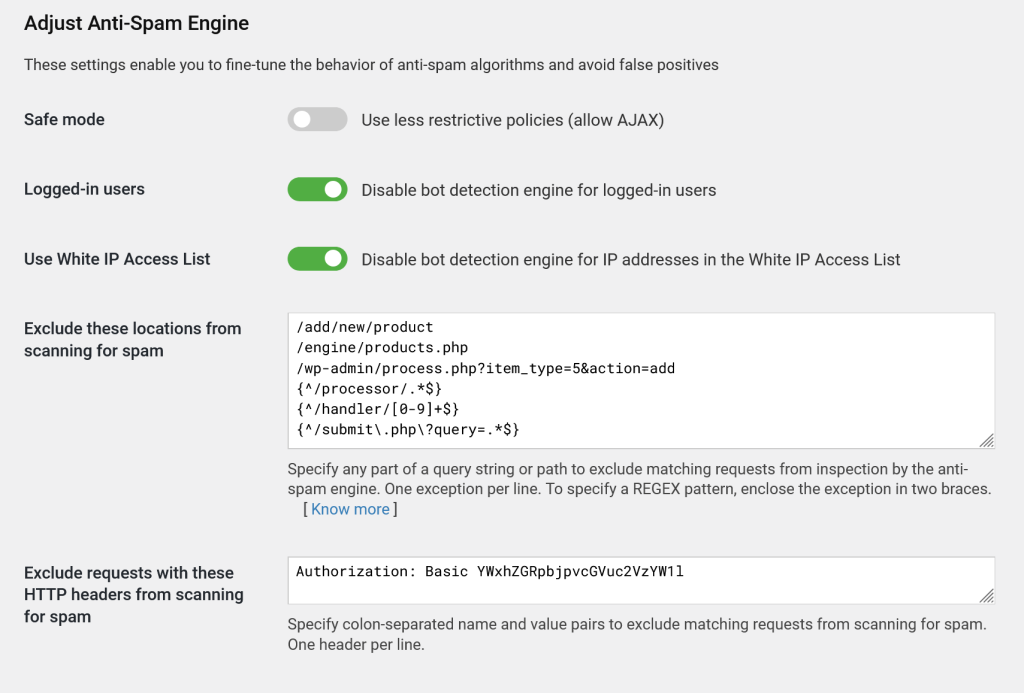
All anti-spam exceptions are configured on the Anti-spam setting page. You can configure two types of exceptions: URL-based and exceptions that check and take into account HTTP Headers.
To set up URL-based exceptions, use the “Exclude these locations from scanning for spam” setting field. You can specify several exceptions, each on a separate line.
Here’s how it works: to exclude a particular request, simply add the path (and, if needed, the query string) for that request in the field. The anti-spam engine will ignore any request where the path contains one of these specified strings, regardless of where it appears in the URL. This way, you can ensure that important requests pass through without being blocked by spam filters.
If you need even more control over exceptions, you can use regular expressions (REGEX) to define more precise URL-based patterns for matching. This can help when you need to exclude requests based on specific variations in paths or query strings. For more tips on using regular expressions and creating effective exceptions, check the additional info below.
Examples of Simple Anti-Spam Exceptions
To help you get started with setting up anti-spam exceptions, here’s a breakdown of some common types of URL paths you can add to the “Exclude these locations from scanning for spam” field.
1. Simple Paths without GET Parameters or Scripts
If you want to exclude specific paths on your WordPress, you can add them as simple strings. The anti-spam engine will skip scanning for any request that contains one of these paths as a substring, no matter where it appears in the URL.
Examples:
"/about""/contact/""/add/new/product"
With these entries, any URL containing these paths will be excluded from spam scanning, regardless of the location within the URI.
2. PHP Script Names without GET Parameters
For cases where you want to exclude specific PHP scripts, simply specify the script and its path. This can be particularly helpful if you have certain scripts that shouldn’t be inspected by the anti-spam engine. The engine will match these scripts by locating the provided filename in the URL.
Examples:
"/index.php""/engine/products.php""search.php"
This type of exceptions is flexible, covering both scripts in the root directory and those nested within subdirectories.
3. Paths with GET Parameters
If your exceptions needs to account for both a specific path and certain query parameters, you can add paths with full GET parameters in the field. The anti-spam engine will only apply the exception if the full string, including parameters, is found in the request URI. This is ideal for precise matching based on both path and query details.
Examples:
"/store/products.php?id=10""/wp/?query=""/wp-admin/process.php?item=5&action=add"
This type of setup ensures that requests with exact parameters are excluded, making it useful for more targeted exceptions.
By using these examples, you can set up various types of exceptions to keep essential requests safe from WP Cerber spam filtering, while maintaining thorough spam protection across other areas of your WordPress.
Advanced Anti-Spam Exceptions with REGEX
For more flexible and powerful control over your anti-spam exceptions, you can use regular expressions (REGEX) to define patterns that match specific types of requests. Using REGEX-based exceptions gives you advanced flexibility to precisely exclude requests that share similar structures or dynamic elements in their paths and/or query parameters.
When you specify a REGEX pattern in the “Exclude these locations from scanning for spam” field, the WP Cerber anti-spam engine will treat it as a flexible match condition. If a request URI matches the pattern, it will be excluded from spam scanning. You can view the full URI of a request on the Traffic Inspector log page.
To specify a REGEX-based exception, enclose your pattern within {}.
Examples of REGEX-Based Anti-Spam Exceptions
Remember to enclose each pattern in {}, so WP Cerber recognizes it as a REGEX expression. Note: To specify a literal dot (.) or a literal question mark (?) in a pattern, you must escape it with a backslash (\) this way: \. and \?.
1. Excluding Paths with Specific Start Points
If you want to exclude all requests that start with a particular path, REGEX lets you match any URI beginning with a specified segment.
- Example:
{^/processor/.*$} - This pattern will exclude any request that starts with
/admin/, regardless of what follows. It’s ideal for directories that include multiple dynamic pages or actions under the same path.
2. Excluding Paths with Numeric IDs
To target paths that contain dynamic numeric IDs, use REGEX to match a series of numbers in specific locations.
- Example:
{^/handler/[0-9]+$} - This pattern will match any path like
/handler/123or/handler/456, where the ID varies but remains numeric. This is helpful for URL that relies on unique numeric identifiers.
3. Excluding Based on Partial Query Parameters
You can also use REGEX to match specific patterns in query strings, making it possible to exclude requests that include certain parameters without needing an exact value.
- Example:
{^/submit\.php\?query=.*$} - This pattern matches any request to
submit.phpwhere thequeryparameter is present, regardless of its actual value.
4. Flexible URL Paths with Optional Parameters
REGEX allows you to account for optional segments within a path or query string, offering more flexibility in defining what gets excluded.
- Example:
{^/products/?(.*)$} - This pattern matches requests to
/productswith or without additional sub-paths, such as/products/detailsor/products/123. Great for broad exceptions across a section of your WordPress.
By using REGEX patterns, you can define anti-spam exceptions tailored to complex or variable requests, giving you precise control over which URLs bypass spam scanning.
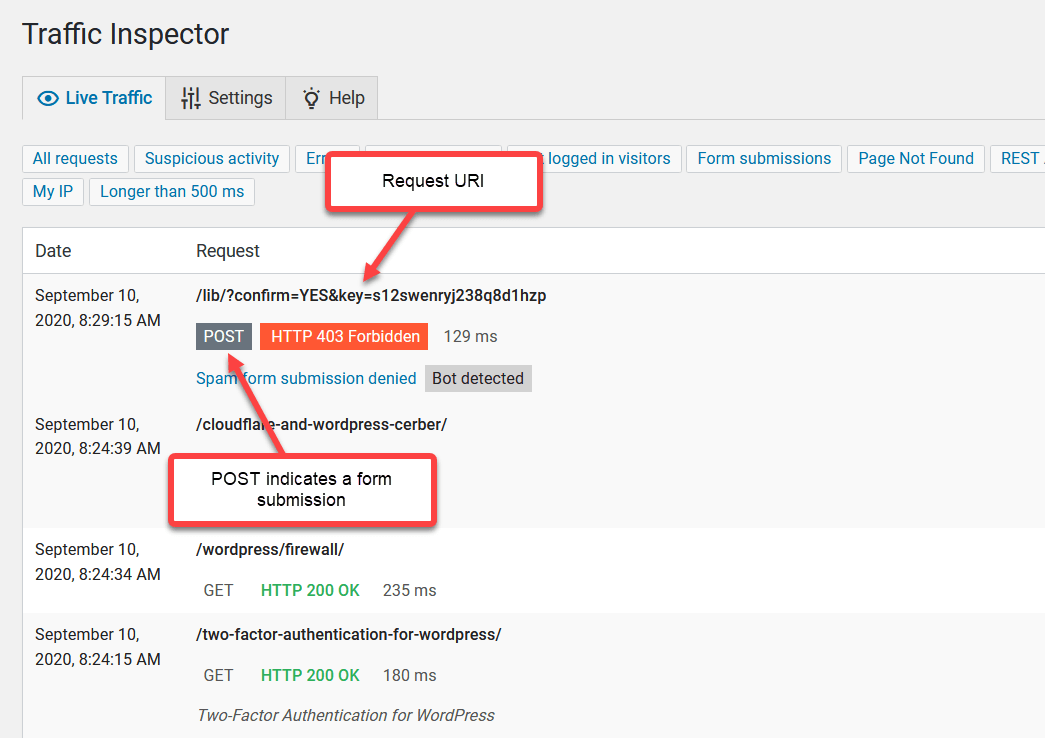
How to identify the Request URI
Go to the Live Traffic admin page. Find a legitimate request you need to whitelist and take its Request URI from the Request column. If your Request URI contains dynamic GET parameters like in the screenshot below, you may need to use a REGEX expression.
How to disable anti-spam on a selected page
To avoid conflicts with third-party forms loaded from an external source and processed on a third-party website, you can configure exceptions for WP Cerber’s anti-spam by disabling its code on selected pages of your website. The list of pages is specified with a PHP constant CERBER_DISABLE_SPAM_FILTER. This constant should be defined in the wp-config.php file. Use a comma-separated string with page (post) IDs. If the list is configured, you see the list of pages on the WP Cerber anti-spam settings admin page. Here is an example of the list definition.
define('CERBER_DISABLE_SPAM_FILTER', '3, 45');You may need to use this feature, if you have HubSpot forms on your website.
See also: How to stop spam user registrations on your WordPress
Have any questions?
If you have a question regarding WordPress security or WP Cerber, ask it in the comments below or find answers on the community forum.
Spotted a bug or glitch?
We’d love to fix it! Share your bug discoveries with us here: Bug Report.