WP Cerber Security 9.1
New features
- A new feature that prevents exposing user’s first name, last name, and ID via an HTTP request with a username (login) in an author_name parameter.
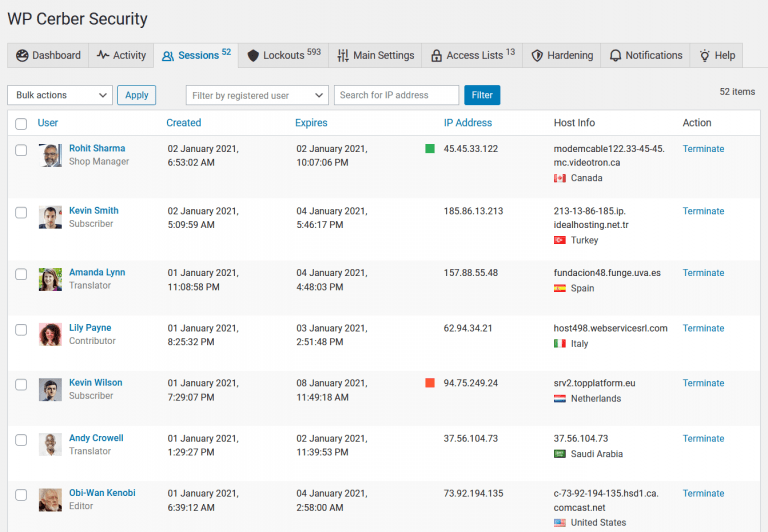
- A new user status report while viewing the user activity/requests log.
Minor improvements
- When renders admin pages, WP Cerber uses the language selected on the user profile.
- Improved the speed of rendering of the “Users” admin page. Reduced the number of HTTP requests if some columns on the page are hidden.
- Implemented support for rate limiting when the integrity scanner retrieves checksum data from remote servers.
- The “Users” admin page got links to the “Sessions” page.
Fixed bugs
- Fixed a bug that allows an attacker to bypass the “Stop user enumeration” feature if it’s enabled (CVE-2022-2939).
- Fixed a bug that produces incorrect messages in the server error log when the WordPress database connection is lost. “PHP Warning: mysqli_real_escape_string() expects parameter 1 to be mysqli, null given…”
- Fixed a bug with not escaping comments in the IP access lists entries.
Download the plugin
https://my.wpcerber.com/downloads/wp-cerber.9.1.zip
Wonder what WP Cerber got in the previous version?
Review the release note for WP Cerber Security 9.0.
How to update WP Cerber
We recommend enabling automatic updates to ensure you always have the latest security features and performance improvements: how to enable automatic updates in the plugin settings.
How to install WP Cerber
New to WP Cerber? Follow this step-by-step guide to install WP Cerber on your WordPress.
Have any questions?
If you have a question regarding WordPress security or WP Cerber, ask it in the comments below or find answers on the community forum.
Spotted a bug or glitch?
We’d love to fix it! Share your bug discoveries with us here: Bug Report.
WordPress Security How To
Next Post
Optimizing export performance
Releases



The Plugin “WP Cerber Security, Anti-spam & Malware Scan” has been removed from wordpress.org.
What is the reson for this ?
A report from a french security expert regarding an unpatched vulnerability. It’s a temporary removal. Actually, it was a bug which is mentioned above, not a vulnerability.
Will it be back up any soon? I was very much enjoying the detail the traffic inspector gives me into some of the specific attack mechanisms people try against my website which is almost empty. I’ve been trying running it alongside Sucuri and Wordfence, but as you might imagine they interfere. I prefer Cerber over Wordfence, so I was a little upset to hear about this.
Yes, sure. In the meantime, you can download the latest version of WP Cerber from our website. Know more: https://wpcerber.com/installation/