WP Cerber Security 8.6.6
We hope that you and your families are safe and well. The last few months have been unprecedented for all of us. Despite the pandemic, we continue to develop and improve WP Cerber Security so you can protect your WordPress more effectively.
An improvement to the layout of the Live Traffic log
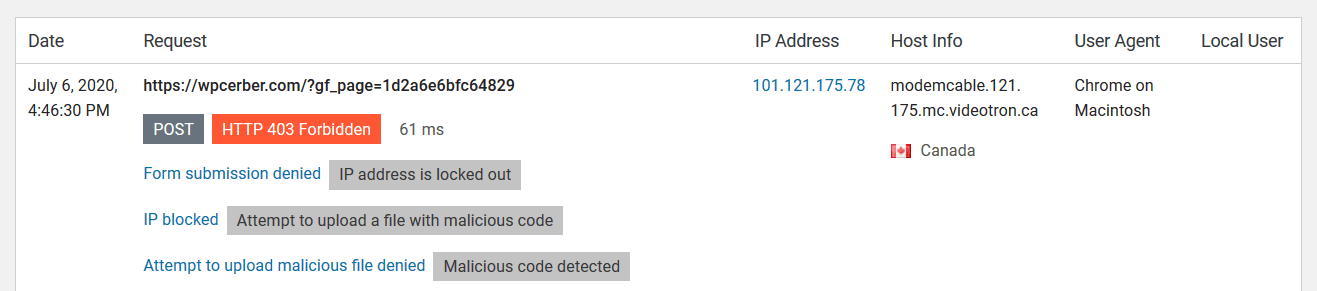
Now all events that are logged during a particular request are shown as an event list sorted in reverse order like log entries. Some rows might look a bit bulky now, but they provide more details for analyzing and troubleshooting, so you will not miss WP Cerber’s firewall actions or form submissions denied by the anti-spam module.
For instance, on a screenshot below, we see that, firstly, WP Cerber identified an attempt to upload a malicious file via a contact form. Then WP Cerber locked out the IP address and finally denied the attempt to submit the form.
New settings for traffic logging
- A new, minimal logging mode has introduced. When it is set, only HTTP requests related to known activities are logged. It’s the default mode now. Use it to reduce server load and the database size. You will always have data on malicious requests and blocked IP addresses with no additional overhead.
- Now you can specify locations (URL Paths) to exclude requests from logging. They can be either exact matches or regular expressions (REGEX). You have to specify the full path from an URL without the website domain for an exact match. To specify a REGEX pattern, enclose a whole line in two braces.
- You can now exclude requests from logging based on the value of the User-Agent (UA) header. If the User-Agent header string contains a specified string, the request is not logged.
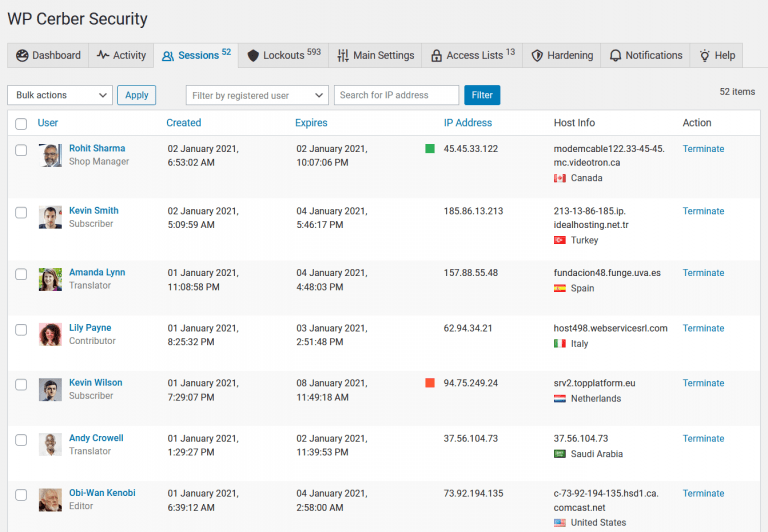
User session management has been improved
- The user sessions page has been optimized for performance and compatibility and now works blazingly fast on websites with thousands of active WordPress user sessions.
- On the user sessions page, you can now search sessions by a user name, email, and the IP address from which a user has logged in.
- If your WordPress is behind a proxy (e.g., Cloudflare), IP addresses of user sessions now are detected more precisely. Incorrect user data provided by WordPress core is not used anymore.
Minor updates
- When you configure the request whitelist in the Traffic Inspector settings, you can now specify rules with or without trailing slash. Previously you may not specify rules without trailing slash.
- Since WP Cerber detects and denies attempts to scan for any kind of vulnerable code on a website (behind the WordPress code), the log label “Probing for vulnerable PHP code” has been changed to “Probing for vulnerable code.”
- The file cerber-news.php is not the part of the plugin anymore. You can safely delete it.
Cloudflare add-on for WP Cerber
A new version of Cloudflare add-on for WP Cerber is available: the performance of the add-on has been optimized.
Wonder what WP Cerber got in the previous version?
Review the release note for WP Cerber Security 8.6.5.
How to update WP Cerber
We recommend enabling automatic updates to ensure you always have the latest security features and performance improvements: how to enable automatic updates in the plugin settings.
How to install WP Cerber
New to WP Cerber? Follow this step-by-step guide to install WP Cerber on your WordPress.
Have any questions?
If you have a question regarding WordPress security or WP Cerber, ask it in the comments below or find answers on the community forum.
Spotted a bug or glitch?
We’d love to fix it! Share your bug discoveries with us here: Bug Report.