WP Cerber Security 8.9.5
This version brings a lot of small but important improvements, performance optimization, and bug fixes. Since WP Cerber 8.9.5 the minimal recommended version is WordPress 5.5. The minimal supported version is still WordPress 4.9. Some features are available in the professional version of WP Cerber.
Activity logging improvements
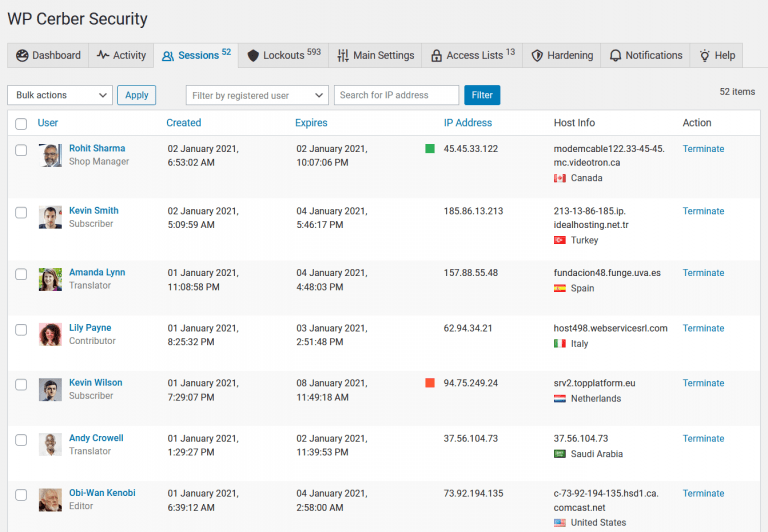
- Logging all user session terminations including those that occurred when an admin manually terminate user sessions or block users via WordPress dashboard admin pages. Previously WP Cerber logs user session terminations occurred due to a configured limit on the number of allowed concurrent user sessions.
- If a user session has been terminated by a website admin, the admin’s name is logged and shown in the Activity log.
- Logging all user password changes including those made on the edit user admin page, and the WooCommerce edit account page. Previously WP Cerber logs changes made on public pages only.
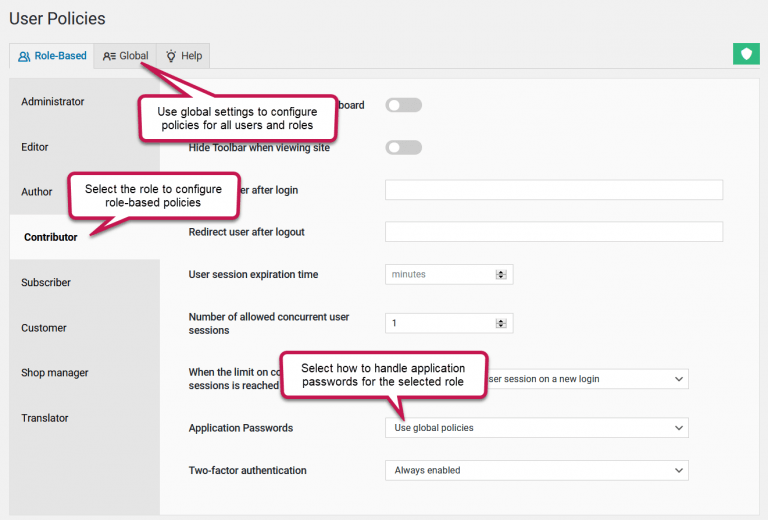
- Logging application passwords changes. They are used to grant access to WordPress REST API. You can restrict or deny using application passwords on the User Policies settings page.
- Logging of reCAPTCHA related events has been revamped and now provides more detailed and consistent information in WP Cerber’s logs.
- New status labels in the activity log: “reCAPTCHA verified” is shown when a user solves reCAPTCHA successfully
- New status labels in the activity log: “Logged out everywhere” is shown when a user has completely logged out on all devices and of all locations.
- Failed reCAPTCHA verifications are logged with form submission events they are linked to.
- A new event is logged: “Password reset request denied”. With possible statuses “reCAPTCHA verification failed”, “User blocked by administrator”, “Username is prohibited”.
- Handling reset of user passwords is improved to support changes in the WordPress core.
New settings for spam protection
- A new setting for WP Cerber’s anti-spam engine: “Disable bot detection engine for IP addresses in the White IP Access List”.
- A new setting for the reCAPTCHA module: “Disable reCAPTCHA for IP addresses in the White IP Access List”.
Fixed bugs
- A cookie-related bug that causes a fatal software error if a user has been deleted or their password has been changed in the WordPress dashboard by the website administrator while the user is being logged in.
- A bug with the WordPress lost password (reset password) form that prevents displaying error messages to a user. It occurs under the following conditions: if visible reCAPTCHA for the form is enabled, “Disable the default reset password error message” is enabled, and the user does not tick the reCAPTCHA checkbox before submitting the form.
- When the limit on the number of allowed concurrent user sessions is set to one, an attempt to log in with the user name and incorrect password terminates the existing session of the user (the user gets logged out by WP Cerber).
- While trying to reset the password for a user blocked by a website administrator, this event is logged as “Password reset requested” instead of “Password reset request denied”.
- While trying to reset the password for a user with a prohibited username, this event is logged as “Password reset requested” instead of “Password reset request denied”.
Wonder what WP Cerber got in the previous version?
Review the release note for WP Cerber Security 8.9.3.
How to update WP Cerber
We recommend enabling automatic updates to ensure you always have the latest security features and performance improvements: how to enable automatic updates in the plugin settings.
How to install WP Cerber
New to WP Cerber? Follow this step-by-step guide to install WP Cerber on your WordPress.
Have any questions?
If you have a question regarding WordPress security or WP Cerber, ask it in the comments below or find answers on the community forum.
Spotted a bug or glitch?
We’d love to fix it! Share your bug discoveries with us here: Bug Report.